EKS Backup and Restore with Velero: Least-Privilege DR for Kubernetes
AWS published a fresh EKS and Velero backup guide on May 12, 2026. The important part is not that Velero exists. Most Kubernetes teams know that. The useful part is building disaster recovery without giving the backup tool a permanent blank check.
That is why this post is intentionally practical. It does not try to turn EKS Velero backup and restore into a product brochure. It treats the announcement, release, or vulnerability as an operating decision: what should a cloud team change, what can wait, what has to be measured, and which guardrails keep the fix from becoming a new source of downtime.
If you are connecting this to the existing BitsLovers library, start with zero-downtime EKS upgrade planning, EKS Auto Mode production operations, CloudWatch Container Insights, EKS RBAC security patterns, SPIFFE and SPIRE workload identity, AWS VPC design patterns. Those articles cover the adjacent platform patterns; this one focuses on Kubernetes disaster recovery using Velero, S3, EBS snapshots, and least-privilege IAM.
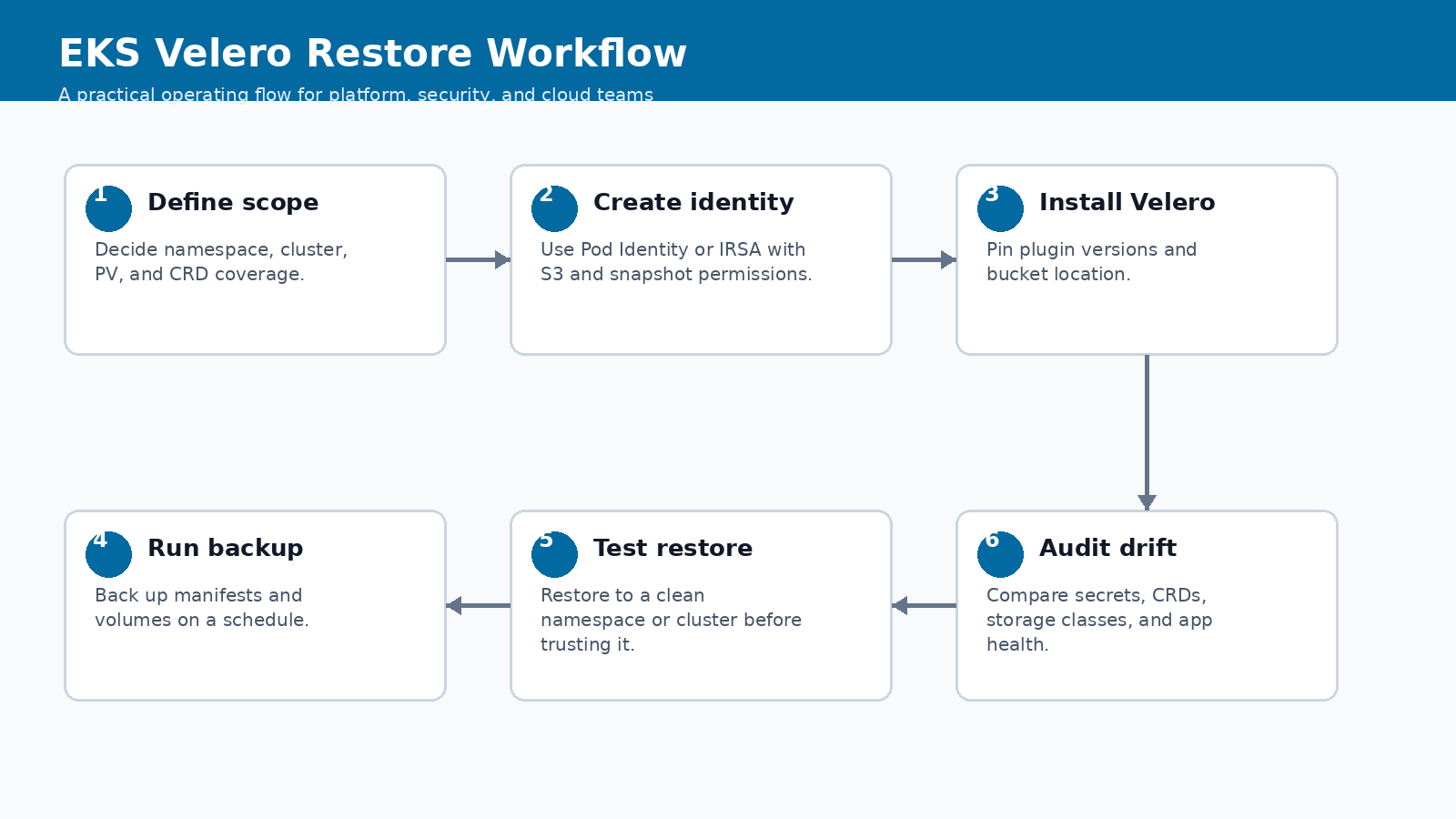
The workflow above is the recommended operating model. It keeps the discussion out of the abstract. You start with the signal, scope the blast radius, implement the smallest useful control, verify the result, and then turn the work into a repeatable runbook. That order matters. A lot of teams jump straight from announcement to tooling. That feels fast, but it usually skips ownership, rollback, and the boring evidence an auditor or incident reviewer will ask for later.
What Changed
The AWS guidance gives EKS teams a current pattern for backing up and restoring cluster resources with Velero. It covers the familiar building blocks: S3 for backup storage, EBS snapshots for persistent volumes, and Kubernetes resources for restore. The decision point is how much access Velero gets and how often you prove restores actually work.
The date matters here because engineering teams already have plenty of stale guidance in their wikis. Treat this as a May 2026 operating note. If a vendor updates the documentation later, update the runbook and leave a revision note in the post. That is not editorial polish; it is how you keep technical content from becoming another unsafe copy-paste source.
Velero stores Kubernetes API objects and coordinates volume snapshots through provider plugins. On AWS, that usually means an S3 bucket for backup metadata and EBS snapshots for persistent volumes. Identity can be handled through EKS Pod Identity or IAM Roles for Service Accounts, depending on how the cluster is built.
Why Platform Teams Should Care
Kubernetes backup is easy to fake. A nightly job can say success while the restore still fails because a CRD is missing, a secret was managed outside the cluster, a storage class name changed, or a namespace policy blocks traffic. DR is not the backup. DR is the restore plus the evidence.
This is also where cost and reliability get mixed together. A feature that looks like a security improvement can increase build time, data scanned, node churn, or operational review effort. A reliability feature can quietly move risk from the service team to the platform team. A new AI workflow can shorten analysis time and still create a governance problem if the identity model is weak. Good engineering writing should name that tradeoff.
For EKS Velero backup and restore, the practical question is not “is this useful?” It is useful. The better question is where the control should live. If it belongs in a one-off project, document it there. If it belongs in the platform baseline, put it in CI, admission control, IAM, observability, or a shared runbook. Most teams get into trouble when they make that boundary implicit.
Operating Baseline
The baseline is a restore test that starts with a blank target and ends with a working application. If the restore requires tribal knowledge, it is not disaster recovery. If the tool needs cluster-admin forever, the security model needs work.
| Backup scope | Use when | Risk to watch |
|---|---|---|
| Namespace backup | Team-owned apps with clear boundaries | Shared CRDs or cluster-scoped dependencies |
| Cluster backup | Platform migration or full-cluster recovery | Restoring stale cluster-wide policy |
| PV snapshots | Stateful apps with EBS volumes | App consistency and crash recovery |
| Manifest-only | Stateless services and GitOps recovery | Missing runtime-generated resources |
The table is deliberately opinionated. It gives you a default answer before the exception shows up. Exceptions are fine; hidden exceptions are not. If someone wants to bypass the default, require a reason, an owner, and an expiration date. That one small rule prevents a lot of permanent “temporary” infrastructure.
Implementation Pattern
The install should make identity and bucket ownership explicit. Do not hide those decisions inside a Helm values file nobody reviews.
velero install \
--provider aws \
--plugins velero/velero-plugin-for-aws:v1.10.0 \
--bucket eks-prod-velero-backups \
--backup-location-config region=us-east-1 \
--snapshot-location-config region=us-east-1 \
--service-account-name velero
velero backup create payments-daily \
--include-namespaces payments \
--snapshot-volumes=true \
--ttl 720h
velero restore create payments-restore-test \
--from-backup payments-daily \
--namespace-mappings payments:payments-restore
The snippet is not meant to be pasted blindly. Use it as the shape of the implementation, then adapt names, account boundaries, tags, and approval gates to your environment. The useful part is the sequence: inspect, constrain, verify, and record evidence. If your process cannot produce evidence, it is not mature enough for production.
Controls, Metrics, And Evidence
A backup system needs operational metrics, not just a green cron line.
| Evidence | Why it matters | Minimum expectation |
|---|---|---|
| Last successful backup age | Shows schedule health | Less than the declared RPO |
| Last successful restore test | Shows DR actually works | Monthly for critical apps |
| Snapshot coverage | Shows stateful workload protection | All declared PVs included or excluded intentionally |
| Identity scope | Shows blast radius | Only required S3, snapshot, and Kubernetes permissions |
Notice that the table separates a control from the evidence. A control without evidence is a hope. Evidence without an owner is a screenshot in a ticket that nobody trusts three months later. Tie each signal to a system that already has retention, access control, and review habits.
Rollout Plan
The first rollout should protect one business application end to end.
- Choose a namespace with one database-backed workload and one stateless workload.
- Create a dedicated backup bucket with lifecycle and access logging.
- Install Velero with scoped identity and a documented ClusterRole. Do not default to permanent cluster-admin.
- Run a restore into a separate namespace and compare service health, config, secrets, and persistent data.
- Promote the pattern to other namespaces only after the first restore test is boring.
This is where teams often overbuild. Start with the smallest production slice that proves the behavior. One non-critical cluster, one runner group, one application namespace, one account, or one data domain is enough. Then widen the blast radius only after you have a rollback path and a metric that proves the change did not make the system worse.
Gotchas
Velero is good, but it does not remove Kubernetes dependency management.
- CRDs must exist before custom resources restore cleanly. Platform CRDs need their own restore order.
- Secrets may come from External Secrets, Parameter Store, Secrets Manager, or manual creation. Know the source of truth.
- Persistent volume snapshots are crash-consistent unless the application participates in quiescing or backup hooks.
- Restoring network policies and admission policies can block the restored app before it starts.
- A backup bucket without lifecycle controls becomes a quiet cost leak.
The uncomfortable lesson is simple: new platform features usually fail at the handoff points. The vendor feature works. The identity mapping is incomplete. The backup restores but not the secret. The scanner finds an issue but nobody owns the fix. The autoscaler drains a zone correctly but the application has a bad disruption budget. These are not edge cases. They are where production work lives.
Security, Reliability, And Cost Tradeoffs
The reliability gain is obvious: you can recover cluster state. The security cost is that a backup controller sees a lot. Least privilege is not optional. The cost tradeoff is snapshot retention. Keep enough history to recover from corruption, but not so much that every volume becomes a permanent bill.
Use a scorecard before rolling the pattern to every team:
| Question | Good answer | Weak answer |
|---|---|---|
| Can we meet RPO? | Backup frequency and restore tests prove it | Cron schedule says daily |
| Can we meet RTO? | Restore timing measured on a clean target | Nobody has timed it |
| Is access scoped? | IAM and RBAC match the backup scope | Cluster-admin because it was easier |
The weak answers are not moral failures. They are just not production answers yet. If your current state is weak, write the gap down, choose the next smallest fix, and keep the change contained until the evidence improves.
First 48 Hours In Practice
The first two days decide whether EKS Velero backup and restore becomes a controlled platform improvement or another half-finished note in a chat thread. I would split the work into three windows: the first hour, the first business day, and the first week. The first hour is about scope. Do not change production yet unless the exposure is obvious. Name the owner, capture the source link, list affected systems, and decide whether this is emergency work or scheduled platform work.
By the end of the first business day, the team should have one working example. That could be one patched runner pool, one restored namespace, one repository review, one governed data domain, one EKS node group, or one shared VPC deployment. The exact target depends on the topic. The point is to choose a small production-shaped slice, not a toy. A lab that has no secrets, no real users, no deployment pressure, and no monitoring will hide the problems that matter.
The first-week goal is repeatability. If the change worked once because a senior engineer babysat it, you have a useful experiment, not a platform pattern. Turn the successful path into a runbook with commands, screenshots, expected output, rollback steps, and escalation rules. Then test it with someone who did not write the first version. That review will expose missing assumptions faster than another hour of polishing.
For Kubernetes disaster recovery using Velero, S3, EBS snapshots, and least-privilege IAM, the review meeting should be short and concrete. Ask what changed, which systems are in scope, which systems are intentionally out of scope, what evidence proves the control works, and what would make the team roll back. If the group cannot answer those five questions, the change is not ready to become a default.
| Owner | Decision to make | Evidence they should demand |
|---|---|---|
| Service owner | Confirms scope and business impact | Accepts or rejects the default action for Namespace backup |
| Platform owner | Turns the pattern into a shared control | Publishes the runbook, dashboard, and rollback path for EKS Velero backup and restore |
| Security owner | Reviews risk and exception handling | Checks that Last successful backup age has usable evidence |
| FinOps or operations owner | Checks cost and toil | Watches whether Last successful restore test creates recurring work |
One practical habit helps a lot: write the rollback criteria before the rollout starts. For EKS Velero backup and restore, a rollback may mean re-enabling an old runner path, restoring a prior IAM policy, pausing an agent workflow, undoing an autoscaling setting, or reverting to a previous storage ownership model. Whatever the answer is, write it down. Operators make better decisions during incidents when the stop condition is already named.
Runbook Artifacts To Keep
A trustworthy runbook is not a wall of prose. It is a small set of artifacts that prove the system can be operated by more than one person. Keep the procedure, the evidence, and the exception list separate. Procedures change often. Evidence grows during exercises and incidents. Exceptions need owners and expiration dates because otherwise they become the real architecture.
| Artifact | What good looks like | Maintenance rule |
|---|---|---|
| Runbook page | One current procedure with commands, owners, and rollback | Update after every exercise or incident |
| Evidence folder | Screenshots, command output, logs, ticket IDs, and query results | Keep according to audit and incident policy |
| Exception register | Every skipped service, account, cluster, repo, or dataset | Owner plus expiration date required |
| Dashboard link | The live view operators use during rollout | Must show the metric in the control table |
The evidence should be boring enough to survive an audit and specific enough to help an engineer at 2 a.m. A command transcript showing shows schedule health is useful. A dashboard screenshot with no time range is not. A ticket that says “verified” is weak. A ticket with the exact source, system, output, owner, and next review date is much stronger.
This also keeps trust resources honest. A blog post can point to AWS, Kubernetes, GitLab, or project documentation, but the local runbook has to say how your team interpreted that source. If the official document changes, the local procedure needs a review. If the source disappears, the team needs a replacement. That is why the trusted resources section at the end of this post is not decorative; it is part of the operating model.
Example Review Questions
Use these questions before making EKS Velero backup and restore a default pattern:
- What is the smallest system where we proved this works with production-like constraints?
- Which team owns the control after the initial rollout is finished?
- Which metric tells us the change helped instead of simply adding process?
- What is the first rollback action if crds must exist before custom resources restore cleanly. platform crds need their own restore order.?
- What exception would we approve, and how long may that exception live?
- Which trusted source would force us to revisit the design if it changed?
Two questions deserve blunt answers. First, does the pattern reduce risk, or does it only move risk to another team? Second, can a new engineer follow the runbook without private context? If the answer to either question is no, keep the rollout narrow.
A Concrete Failure Scenario
Imagine the team accepts the default action for namespace backup but ignores cluster backup. At first, the rollout looks successful. The dashboard turns green. The announcement is written. Then the first exception arrives. A service owner cannot meet the deadline, a cluster has an unusual constraint, or a repository breaks in a way the shared workflow did not predict. Without an exception register, the team handles that case in a side conversation. Two weeks later nobody remembers whether the exception was temporary.
That is the failure mode this article is trying to avoid. The technology can be good and the rollout can still decay. The fix is not more meetings. The fix is a small operating loop: define the default, record the exception, attach an owner, set an expiration date, and review the evidence. This is simple, but it is not optional for production work.
Secrets may come from External Secrets, Parameter Store, Secrets Manager, or manual creation. Know the source of truth. That gotcha should shape the rollout. Put it in the runbook as a check, not as a footnote. If a future operator has to rediscover it during an outage or audit review, the article failed to become operational knowledge.
When To Use This
Use this pattern when you have EKS workloads where GitOps alone cannot reconstruct runtime state, persistent volumes, or cluster-scoped dependencies.
Do not use it when the workload is purely stateless, fully recreated from Git, and has no runtime state worth preserving. That boundary is important because the wrong abstraction can make a simple system harder to operate. Sometimes the best platform decision is to leave a feature out of the shared baseline and document a local exception instead.
Trusted Resources
These are the sources I would keep next to the runbook:
- AWS EKS Velero backup and restore blog
- Velero documentation
- EKS Pod Identity
- Amazon EBS snapshots
- Kubernetes persistent volumes
- AWS S3 lifecycle configuration
I am intentionally marking one uncertainty: plugin versions, Pod Identity support, and restore behavior should be checked against the current Velero and EKS documentation before production rollout. Treat the article as an operating guide, not as a replacement for the vendor documentation. The source links above are the authority when a limit, feature state, or mitigation changes.
The Practical Takeaway
A backup that has never been restored is a story. Velero becomes DR only after the restore works under least privilege.




Comments