Dirty Frag and Fragnesia: Linux LPE Response Plan for Cloud Fleets
On May 7, 2026, the Dirty Frag disclosure put Linux local privilege escalation back on the priority board. On May 13, Fragnesia followed. That one-week rhythm is enough to change the response from “watch the advisory” to “prove every long-lived Linux host can be patched and rebooted on purpose.”
That is why this post is intentionally practical. It does not try to turn Dirty Frag and Fragnesia into a product brochure. It treats the announcement, release, or vulnerability as an operating decision: what should a cloud team change, what can wait, what has to be measured, and which guardrails keep the fix from becoming a new source of downtime.
If you are connecting this to the existing BitsLovers library, start with the Copy Fail response playbook, container runtime security on EKS, SBOM and signing controls in GitLab CI, Amazon Inspector vulnerability management, GitLab runner tag isolation, zero-downtime EKS upgrades. Those articles cover the adjacent platform patterns; this one focuses on Linux local privilege escalation response across cloud hosts, Kubernetes nodes, and CI runners.
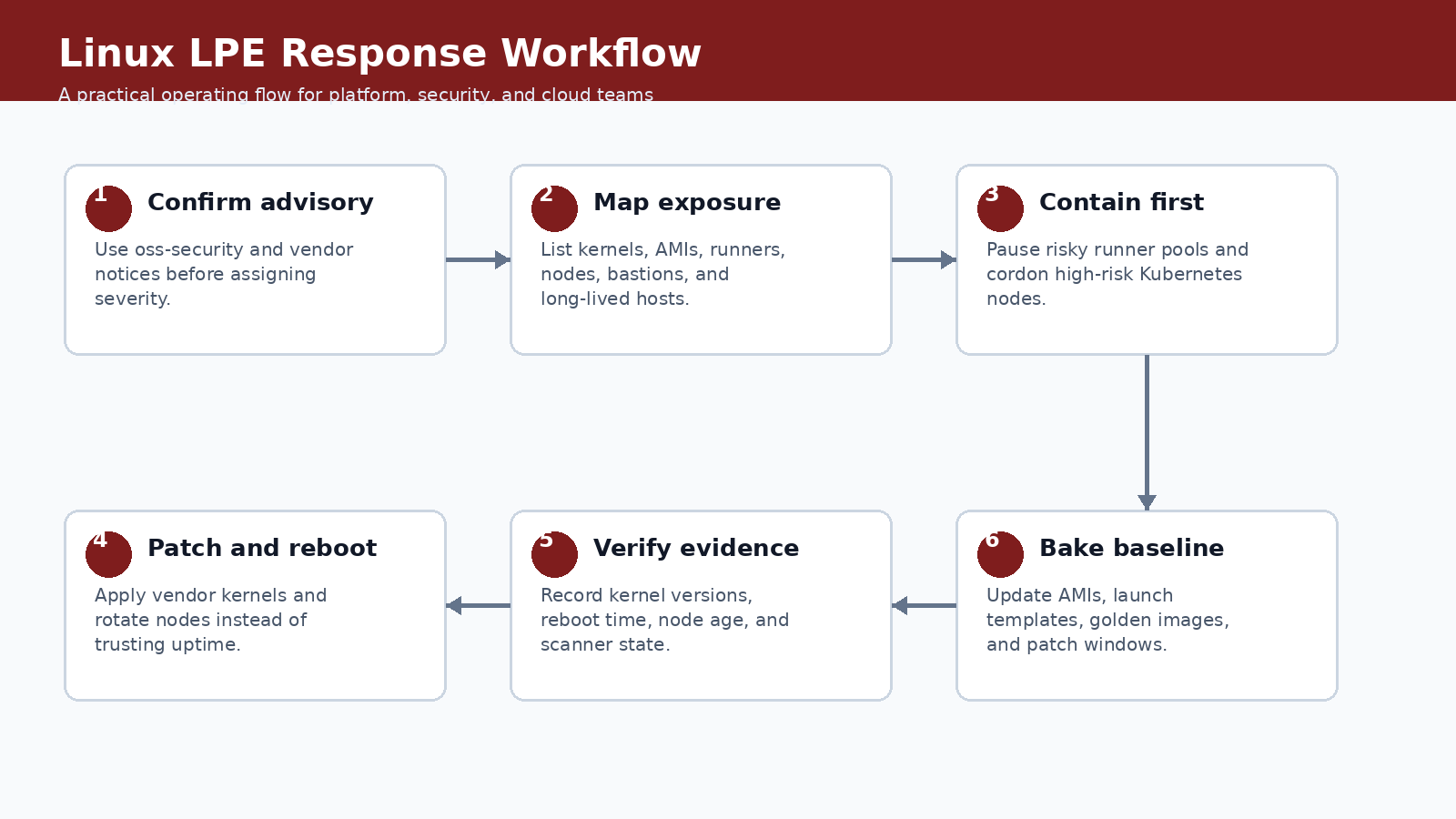
The workflow above is the recommended operating model. It keeps the discussion out of the abstract. You start with the signal, scope the blast radius, implement the smallest useful control, verify the result, and then turn the work into a repeatable runbook. That order matters. A lot of teams jump straight from announcement to tooling. That feels fast, but it usually skips ownership, rollback, and the boring evidence an auditor or incident reviewer will ask for later.
What Changed
Dirty Frag and Fragnesia are not remote cloud account takeovers. They are local privilege escalation signals. That distinction matters. An attacker usually needs some foothold first: a shell on a CI runner, a compromised container workload with too much host access, a developer bastion, or an unpatched VM running a workload nobody has touched in months. But once a local bug is reliable enough, the weak point becomes fleet hygiene, not the exploit itself.
The date matters here because engineering teams already have plenty of stale guidance in their wikis. Treat this as a May 2026 operating note. If a vendor updates the documentation later, update the runbook and leave a revision note in the post. That is not editorial polish; it is how you keep technical content from becoming another unsafe copy-paste source.
The safest public writing about these issues should stay defensive. You do not need exploit mechanics to run a useful response. You need affected-kernel inventory, vendor patch status, reboot proof, runner isolation, node rotation, and a short list of systems that cannot be patched inside the emergency window.
Why Platform Teams Should Care
Cloud teams tend to underestimate local privilege bugs because IAM and network controls get more attention. That is a mistake. A local kernel bug can turn a small application compromise into host-level control. In Kubernetes, host-level control can expose kubelet credentials, mounted service-account tokens, local logs, or node-level network position. In CI, it can expose build secrets and signing keys. In a bastion, it can erase the line between a normal user shell and privileged maintenance access.
This is also where cost and reliability get mixed together. A feature that looks like a security improvement can increase build time, data scanned, node churn, or operational review effort. A reliability feature can quietly move risk from the service team to the platform team. A new AI workflow can shorten analysis time and still create a governance problem if the identity model is weak. Good engineering writing should name that tradeoff.
For Dirty Frag and Fragnesia, the practical question is not “is this useful?” It is useful. The better question is where the control should live. If it belongs in a one-off project, document it there. If it belongs in the platform baseline, put it in CI, admission control, IAM, observability, or a shared runbook. Most teams get into trouble when they make that boundary implicit.
Operating Baseline
Start with an inventory you can defend. For AWS-heavy environments, combine Systems Manager inventory, Inspector findings, AMI version checks, EKS node group age, and GitLab runner registration data. If a host is not in inventory, treat that as a separate incident. Unknown Linux is worse than vulnerable Linux because you cannot even prove the patch state.
| Fleet area | Default action | Evidence to keep |
|---|---|---|
| EKS managed nodes | Roll a fresh node group or recycle nodes after AMI patching | Node image ID, kernel version, drain event, replacement time |
| Self-managed EC2 | Patch through SSM Patch Manager and require reboot proof | Patch baseline result, reboot timestamp, Inspector status |
| GitLab runners | Pause shared runners until host image and executor isolation are verified | Runner version, image digest, secret scope review |
| Bastions | Patch immediately or replace; do not defer because user count is low | Session logs, kernel version, access review |
The table is deliberately opinionated. It gives you a default answer before the exception shows up. Exceptions are fine; hidden exceptions are not. If someone wants to bypass the default, require a reason, an owner, and an expiration date. That one small rule prevents a lot of permanent “temporary” infrastructure.
Implementation Pattern
A useful first pass is a narrow inventory query. This is not a replacement for vendor advisories, but it tells you which instances need a human decision today.
aws ssm describe-instance-information \
--query 'InstanceInformationList[].{Id:InstanceId,Platform:PlatformName,Version:PlatformVersion,LastPing:LastPingDateTime}' \
--output table
aws inspector2 list-findings \
--filter-criteria '{"resourceType":[{"comparison":"EQUALS","value":"AWS_EC2_INSTANCE"}],"findingStatus":[{"comparison":"EQUALS","value":"ACTIVE"}]}' \
--query 'findings[].{Severity:severity,Title:title,Instance:resources[0].id}' \
--output table
kubectl get nodes -o custom-columns=NAME:.metadata.name,KERNEL:.status.nodeInfo.kernelVersion,IMAGE:.status.nodeInfo.osImage
The snippet is not meant to be pasted blindly. Use it as the shape of the implementation, then adapt names, account boundaries, tags, and approval gates to your environment. The useful part is the sequence: inspect, constrain, verify, and record evidence. If your process cannot produce evidence, it is not mature enough for production.
Controls, Metrics, And Evidence
The metrics are intentionally boring. During a kernel response, boring is good. You want timestamps, versions, and proof that old capacity left the fleet.
| Control | Metric | Target |
|---|---|---|
| Kernel patch state | Percent of Linux hosts on vendor-fixed kernel | 100 percent for internet-facing and build fleets first |
| Reboot proof | Hosts patched but not rebooted | 0 after emergency window |
| Runner isolation | Shared runners with broad secrets | 0 for untrusted project groups |
| Node age | EKS nodes older than patched AMI | 0 in production pools |
Notice that the table separates a control from the evidence. A control without evidence is a hope. Evidence without an owner is a screenshot in a ticket that nobody trusts three months later. Tie each signal to a system that already has retention, access control, and review habits.
Rollout Plan
Treat the response as a two-track rollout: emergency containment for risky entry points, then image hygiene for the fleet.
- Freeze or isolate shared CI runner pools that execute untrusted code until their host image is patched.
- Cordon and drain a small set of Kubernetes nodes first. Watch pod disruption behavior before rotating a full node group.
- Patch EC2 instances through SSM where possible. Replace snowflake servers that cannot report patch state.
- Update launch templates, AMI pipelines, and base container host images before declaring the incident closed.
- Write down every exception with an owner and an expiration date. No owner means the host should not stay in production.
This is where teams often overbuild. Start with the smallest production slice that proves the behavior. One non-critical cluster, one runner group, one application namespace, one account, or one data domain is enough. Then widen the blast radius only after you have a rollback path and a metric that proves the change did not make the system worse.
Gotchas
The dangerous parts are usually process mistakes, not the kernel commands.
- A patched package without a reboot can still leave the old kernel running. Check the running kernel, not just package metadata.
- Kubernetes draining can be blocked by bad PodDisruptionBudgets. Test one node pool before rotating everything.
- Shared CI runners are high-risk because they intentionally execute code from many projects. Secrets must be scoped as tightly as the executor.
- Golden images can reintroduce the vulnerable kernel if the AMI pipeline is not updated before autoscaling replaces capacity.
- Inspector and other scanners can lag behind vendor advisories. Use them as evidence, not as the only source of truth.
The uncomfortable lesson is simple: new platform features usually fail at the handoff points. The vendor feature works. The identity mapping is incomplete. The backup restores but not the secret. The scanner finds an issue but nobody owns the fix. The autoscaler drains a zone correctly but the application has a bad disruption budget. These are not edge cases. They are where production work lives.
Security, Reliability, And Cost Tradeoffs
The reliability risk is node churn. The security risk is leaving long-lived hosts untouched. The cost risk is replacing too much capacity at once and forcing on-demand spillover. The right answer is staged rotation with hard deadlines. Security gets the deadline; reliability gets the rollout shape.
Use a scorecard before rolling the pattern to every team:
| Question | Good answer | Weak answer |
|---|---|---|
| Can we prove every Linux host is in inventory? | SSM or another source lists host, kernel, owner, and last check-in | Static spreadsheet or tribal knowledge |
| Can we rotate nodes without downtime? | PDBs, readiness probes, and capacity buffers tested | Drain command tried for the first time during emergency |
| Can we control runner blast radius? | Runner pools separated by trust level and secret scope | One shared runner group for everything |
The weak answers are not moral failures. They are just not production answers yet. If your current state is weak, write the gap down, choose the next smallest fix, and keep the change contained until the evidence improves.
First 48 Hours In Practice
The first two days decide whether Dirty Frag and Fragnesia becomes a controlled platform improvement or another half-finished note in a chat thread. I would split the work into three windows: the first hour, the first business day, and the first week. The first hour is about scope. Do not change production yet unless the exposure is obvious. Name the owner, capture the source link, list affected systems, and decide whether this is emergency work or scheduled platform work.
By the end of the first business day, the team should have one working example. That could be one patched runner pool, one restored namespace, one repository review, one governed data domain, one EKS node group, or one shared VPC deployment. The exact target depends on the topic. The point is to choose a small production-shaped slice, not a toy. A lab that has no secrets, no real users, no deployment pressure, and no monitoring will hide the problems that matter.
The first-week goal is repeatability. If the change worked once because a senior engineer babysat it, you have a useful experiment, not a platform pattern. Turn the successful path into a runbook with commands, screenshots, expected output, rollback steps, and escalation rules. Then test it with someone who did not write the first version. That review will expose missing assumptions faster than another hour of polishing.
For Linux local privilege escalation response across cloud hosts, Kubernetes nodes, and CI runners, the review meeting should be short and concrete. Ask what changed, which systems are in scope, which systems are intentionally out of scope, what evidence proves the control works, and what would make the team roll back. If the group cannot answer those five questions, the change is not ready to become a default.
| Owner | Decision to make | Evidence they should demand |
|---|---|---|
| Service owner | Confirms scope and business impact | Accepts or rejects the default action for EKS managed nodes |
| Platform owner | Turns the pattern into a shared control | Publishes the runbook, dashboard, and rollback path for Dirty Frag and Fragnesia |
| Security owner | Reviews risk and exception handling | Checks that Kernel patch state has usable evidence |
| FinOps or operations owner | Checks cost and toil | Watches whether Reboot proof creates recurring work |
One practical habit helps a lot: write the rollback criteria before the rollout starts. For Dirty Frag and Fragnesia, a rollback may mean re-enabling an old runner path, restoring a prior IAM policy, pausing an agent workflow, undoing an autoscaling setting, or reverting to a previous storage ownership model. Whatever the answer is, write it down. Operators make better decisions during incidents when the stop condition is already named.
Runbook Artifacts To Keep
A trustworthy runbook is not a wall of prose. It is a small set of artifacts that prove the system can be operated by more than one person. Keep the procedure, the evidence, and the exception list separate. Procedures change often. Evidence grows during exercises and incidents. Exceptions need owners and expiration dates because otherwise they become the real architecture.
| Artifact | What good looks like | Maintenance rule |
|---|---|---|
| Runbook page | One current procedure with commands, owners, and rollback | Update after every exercise or incident |
| Evidence folder | Screenshots, command output, logs, ticket IDs, and query results | Keep according to audit and incident policy |
| Exception register | Every skipped service, account, cluster, repo, or dataset | Owner plus expiration date required |
| Dashboard link | The live view operators use during rollout | Must show the metric in the control table |
The evidence should be boring enough to survive an audit and specific enough to help an engineer at 2 a.m. A command transcript showing percent of linux hosts on vendor-fixed kernel is useful. A dashboard screenshot with no time range is not. A ticket that says “verified” is weak. A ticket with the exact source, system, output, owner, and next review date is much stronger.
This also keeps trust resources honest. A blog post can point to AWS, Kubernetes, GitLab, or project documentation, but the local runbook has to say how your team interpreted that source. If the official document changes, the local procedure needs a review. If the source disappears, the team needs a replacement. That is why the trusted resources section at the end of this post is not decorative; it is part of the operating model.
Example Review Questions
Use these questions before making Dirty Frag and Fragnesia a default pattern:
- What is the smallest system where we proved this works with production-like constraints?
- Which team owns the control after the initial rollout is finished?
- Which metric tells us the change helped instead of simply adding process?
- What is the first rollback action if a patched package without a reboot can still leave the old kernel running. check the running kernel, not just package metadata.?
- What exception would we approve, and how long may that exception live?
- Which trusted source would force us to revisit the design if it changed?
Two questions deserve blunt answers. First, does the pattern reduce risk, or does it only move risk to another team? Second, can a new engineer follow the runbook without private context? If the answer to either question is no, keep the rollout narrow.
A Concrete Failure Scenario
Imagine the team accepts the default action for eks managed nodes but ignores self-managed ec2. At first, the rollout looks successful. The dashboard turns green. The announcement is written. Then the first exception arrives. A service owner cannot meet the deadline, a cluster has an unusual constraint, or a repository breaks in a way the shared workflow did not predict. Without an exception register, the team handles that case in a side conversation. Two weeks later nobody remembers whether the exception was temporary.
That is the failure mode this article is trying to avoid. The technology can be good and the rollout can still decay. The fix is not more meetings. The fix is a small operating loop: define the default, record the exception, attach an owner, set an expiration date, and review the evidence. This is simple, but it is not optional for production work.
Kubernetes draining can be blocked by bad PodDisruptionBudgets. Test one node pool before rotating everything. That gotcha should shape the rollout. Put it in the runbook as a check, not as a footnote. If a future operator has to rediscover it during an outage or audit review, the article failed to become operational knowledge.
When To Use This
Use this pattern when you run Linux hosts that execute untrusted code, carry production credentials, host Kubernetes workloads, or act as administrative entry points.
Do not use it when the system is an isolated lab with no production data, no persistent credentials, and no route to shared infrastructure. That boundary is important because the wrong abstraction can make a simple system harder to operate. Sometimes the best platform decision is to leave a feature out of the shared baseline and document a local exception instead.
Trusted Resources
These are the sources I would keep next to the runbook:
- Dirty Frag oss-security disclosure
- Fragnesia oss-security disclosure
- AWS Systems Manager Patch Manager
- Amazon Inspector EC2 scanning
- Kubernetes drain nodes safely
- GitLab Runner security
I am intentionally marking one uncertainty: kernel advisories and downstream vendor package status can change quickly during the first days of a vulnerability response. Treat the article as an operating guide, not as a replacement for the vendor documentation. The source links above are the authority when a limit, feature state, or mitigation changes.
The Practical Takeaway
The patch is only half the work. The real win is proving that every Linux fleet has an owner, a reboot path, and a way to stop old images from coming back.




Comments